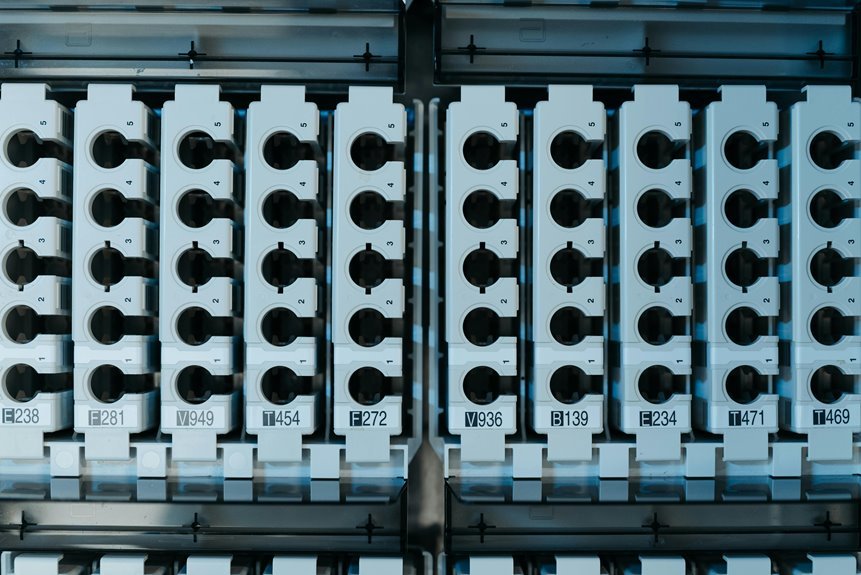
In examining the Mirrorwake Report on Shattered Nodes, you’ll uncover critical vulnerabilities that threaten digital infrastructures. These codes—15413051, 1204472150, 1274945564, 3301270279, and 1172053283—represent more than just identifiers; they highlight shattered connections that disrupt communication. Understanding their implications is essential for fostering resilience and ensuring data integrity. What strategies can organizations implement to mitigate these risks effectively? The answers may be more complex than you think.
Understanding the Significance of Shattered Nodes
As you delve into the concept of shattered nodes, it’s essential to grasp their significance within the broader context of network dynamics.
These shattered connections expose underlying node vulnerabilities, disrupting communication pathways.
Understanding how these fractures occur enables you to devise strategies for resilience.
Analyzing the Impact on Node Stability
When shattered nodes disrupt a network, they significantly impact overall node stability.
You’ll notice a decline in node performance, as the interconnected structure falters under data disruption. This instability can lead to cascading failures, affecting not just individual nodes but the entire system.
Maintaining awareness of these vulnerabilities is crucial for ensuring a resilient network that upholds your desire for freedom and autonomy.
Trends in Digital Infrastructure Resilience
While the landscape of digital infrastructure continues to evolve, resilience has emerged as a critical focus for organizations aiming to safeguard their operations against disruptions.
You’ll find that integrating cloud security measures and establishing network redundancy are key trends driving this resilience.
These strategies not only enhance operational continuity but also empower businesses to adapt swiftly to unforeseen challenges, ensuring greater freedom in their digital engagements.
Strategies for Enhancing Data Integrity
Ensuring data integrity is crucial for organizations that rely on accurate information to drive decision-making and maintain operational efficiency.
Implementing robust data validation processes, utilizing encryption techniques, and establishing effective error detection mechanisms are essential steps.
Additionally, regular backup solutions safeguard against data loss, enhancing your overall data integrity strategy.
Prioritizing these measures empowers you to operate confidently and securely in a data-driven environment.
Conclusion
In summary, addressing shattered nodes is crucial for cultivating a resilient and reliable digital infrastructure. By prioritizing proactive measures, you can prevent potential pitfalls and promote stability. Implementing innovative strategies for data integrity not only safeguards your systems but also secures seamless communication. Remember, with vigilance and versatility, you can transform vulnerabilities into victories, ensuring your organization thrives amidst turmoil. Let’s fortify our foundations and foster a future of uninterrupted connectivity and operational excellence.